Threat Management
At a Glance
- Threat management appliance that provides an extra layer of security to a network to help combat against various cyber attacks
- Subscription-based anti-virus software scans for viruses in emails, when browsing the web or communicating with other applications
- Detects unauthorized access and unwanted intrusions
- Prevents access to malicious web sites
- URL filtering capabilities block access to harmful or non-business related sites or keywords
- Protects against the spread of viruses by limiting use of applications that freely exchange information
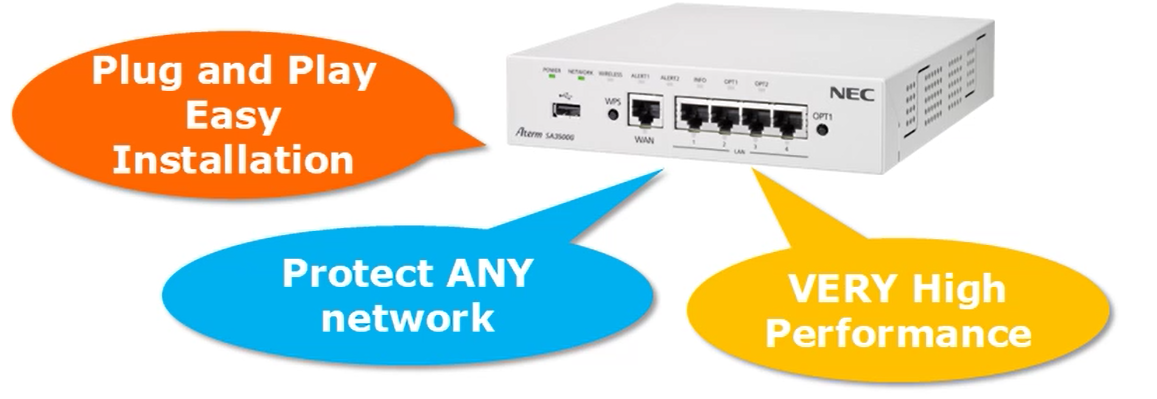
- Easy installation and configuration
- Provides up to 700 Mbps throughput even when security is enabled
- Works on any network
Solution
NEC’s Unified Threat Management solution is a subscription-based service that offers the latest in threat management through an easily installed device that adds extra security to your network. As it sits between your router and your business’s network, it combines multiple functions to prevent employees from accidently accessing dangerous sites, thwart unauthorized access from the Internet, and detects/cleanses viruses included in files attached to emails sent or received or downloaded from the web.
Threat Management Functions
- Anti – Virus – This neutralizes programs containing virus and dangerous code. Monitors communications of the homepage, sending and receiving mails, communication of other applications, and renders the file harmless when the virus or dangerous code is included in the file.
- Intrusion Prevention – This improves the level of security measure by detecting the defending the company network’s intrusions and attacks.
- Web Guard – Guards access to dangerous sites such as phishing sites and sites that are infected by browsing.
- URL Filtering – This limits the browsing by filtering the category of web site. This will block access to harmful or non – business related sites.
- URL Keyword Filtering – By registering a specific character string in advance, access to the page of the URL containing the registered character string is blocked.
- Application Guard – This restricts the use of applications that many unspecified individuals can exchange information such as file exchange software, video sharing applications, messenger application, etc. This prevents virus infection and information leakage from partners malicious parties who do not take security measures.
- Security Log and Email Notifications – All of the threat management functions mentioned above generate log messages when a threat is detected. The information captured is detection date, name of the detecting function, detection contents and the Internet Protocol address of the terminal to be detected. The Security Log’s monthly statistics can be scheduled to be sent to the administrator and saved for future reference. When a threat is detected, not only is a log of it saved, but an email notification is sent out to appropriate personnel that one has occurred.
High-Speed Transmission – With all of the combined security functions of the UTM, you would probably assume it would affect network throughput. Typically, when adding security measures to a network, the speed of it tends to slow down. The UTM is built to enhance network security while not impeding the transmission rate of your network. Its 700 Mbps highspeed throughput is achieved by utilizing a high-speed security engine. Enhancing security no longer means a slower network.
Ease of Installation and Configuration – Installing the UTM in your network is as easy as connecting the WAN port to your router and the LAN port to your network. Once connected, the easy to use web set up allows you to customize threat detection according to your business’s requirements.
Display of Daily Statistics Data
Below you will see a daily report that highlights the stats of what the Theat Managment data accomplishes during the day.
For example: If you look at the box on the top right you will see that there were 1,165 applications that were examined on this day.
* Detail reports are available and all reports can be exported.